IASbaba's Daily Current Affairs Analysis, IASbaba's Daily Current Affairs July 2015, UPSC
Archives
IASbaba’s Daily Current Affairs- 07th July, 2015
ECONOMICS
No immunity for wealth generated from graft
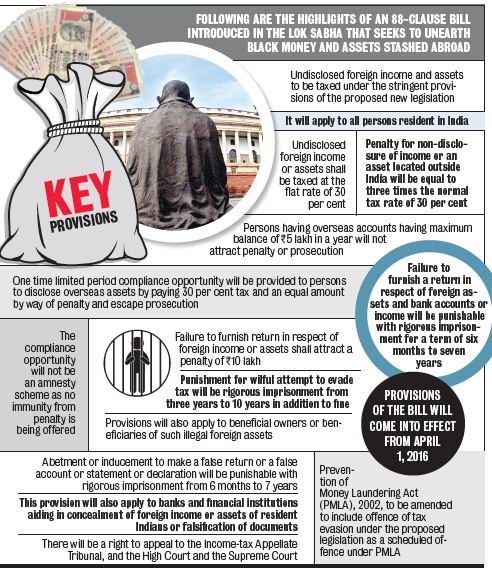
The advantage of declaring foreign assets under the compliance window in the new black money law will not be available to those who were served notices by tax authorities before July 1.
Who are not eligible?
- Those persons whose cases are pending before an appellate authority will also not be eligible for the one-time offer, the Ministry said in FAQs on the new Black Money Act.
- “The declarant is not entitled to re-open any assessment or reassessment made under the Income Tax Act,” it clarified.
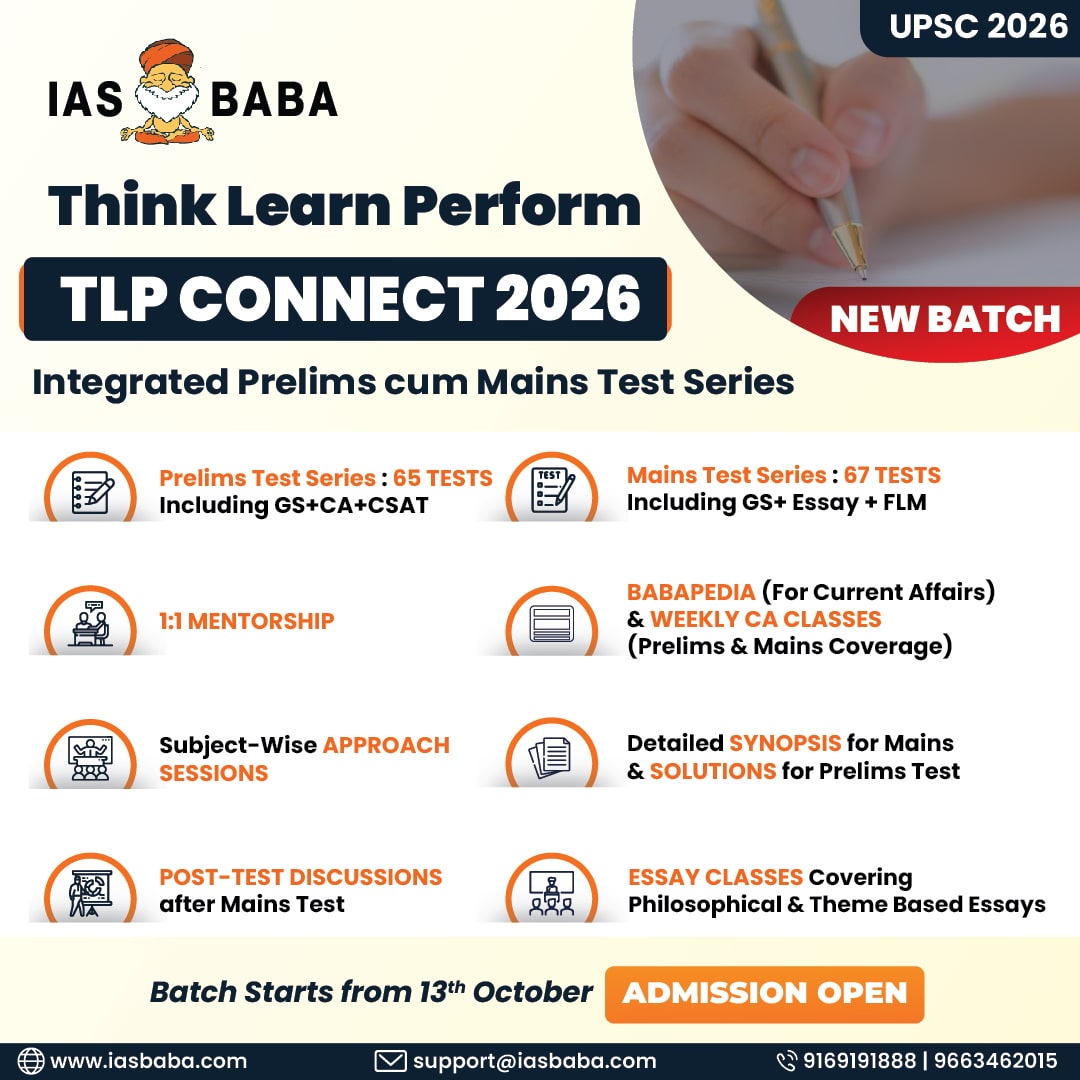
What are the other Important Provisions of Black Money Act?
- Declarations by persons against whom the government has prior information will be dealt with under the Income Tax Act and not under the stringent black money law.
- The one-time 90-day compliance window is being provided to foreign asset holders to come clean under the new law.
- Holders of foreign assets availing the compliance window will have to pay 30 per cent tax and an equivalent amount of penalty by December 31.
How the PMLA linked to this?
- The government will give immunity from prosecution under FEMA, Prevention of Money Laundering Act and four other laws to persons declaring undisclosed foreign assets under the compliance window.
- The offence of willful attempt to evade tax will also not be an offence under the Prevention of Money Laundering Act (PMLA).
- Disclosures made will enjoy immunity from prosecution under the Income-tax Act, Wealth Tax Act, FEMA, Companies Act and Customs Act.
Connecting the Dots
- In what way black money act is related to Prevention of Money Laundering Act?
- Write a note on Black Money Compliance Window.
- Where does the wealth generated from corruption go?
Islamic State guidelines to avoid online surveillance
Stepping up their online propaganda war, proponents of the Islamic State have now come up with guidelines for followers to thwart attempts by foreign intelligence agencies to track them down.
What hints can be traced from these guidelines?
- Launched about a week ago and circulated through Twitter, the four-page guidelines suggest employing a tool initially developed by the United States Naval Research Laboratory in the mid-1990s.
- “Use TOR [acronym for The Onion Router]. Even if you are in IS territory, use TOR so as to not reveal your IP address and thus, location as the ‘kuffar’ coalition can use this information for military means,” says the IS release titled “Collation of social media tips & hints to help muwahideen & new users” created on website justpaste.in.
- Those outside the IS territory “must understand that their accounts can be followed and tracked by security agencies in order to arrest them and other muwahideen they interact with online…”
Is it possible for a lone wolf in Cyberspace?
- An aspiring terrorist can use the Internet to find everything from instructions on how to build a bomb to diagrams of civic buildings that could be potential targets.
- Websites, Facebook pages, YouTube videos and Twitter postings all provide venues for cultivating extremism that was once possible only through clandestine face-to-face meetings.
- In the 2013 Boston Marathon bombing, for example, the lone-wolf killers used an explosive device they had learned to make on the Internet.
What anonymity this ensures?
- The free software works on a large network of volunteer-operated servers. It is said to be a safer way of ensuring anonymity on the Internet, and facilitates access to blocked sites, hides user IP address and encrypts contents.
- The IS guidelines warn that even TOR maintained by a U.S.-based non-profit Organisation is not foolproof and that more precautions need to be taken to ensure anonymity.
IAS BABA’S View
- “Lone wolf” terrorism is often cited as the biggest terrorist threat today.
- This is particularly true at a time when surveillance technology and society’s reliance on digital information are evolving much faster than U.S. laws.
- The war on terrorism especially on lone-wolf terrorism requires new countermeasures.
- But also a well-defined set of rules and guidelines.
Connecting the dots
- What is Online Surveillance?
- What measures should India adopt to ensure safety of Surveillance Technology?
Tibet poised to become part of ‘Belt and Road’ initiative
China’s efforts to forge a new social contract with people of the Tibet Autonomous Region (TAR), based on generous subsidies, jobs and education, appear to be paying off, with the booming Tibetan capital showing little signs of remembering the Dalai Lama on the eve of his eightieth birthday

What is Belt and Road Initiative?
- China announces plans to boost the road, rail and maritime trade by creating economic corridors and investing nearly $900bn (£586bn) in countries along the route.
- The country is mulling six economic corridors to better connect Asia and Europe, with funding from the Asian Infrastructure Investment Bank and the Silk Road Fund, for the project that is known in China as “One Road, One Belt”
Why India needs to be wary of China’s ambitious belt and road initiative?
- India looks at this Chinese initiative suspiciously.
- The Indian suspicion has been fueled further as strategic circles in New Delhi view the China-Pakistan Economic Corridor (CPEC) and the Bangladesh-China-India-Myanmar (BCIM) Economic Corridor as nothing but microcosms of the Chinese Belt and Road Initiative.
What type of Nexus this creates between China and Pakistan?
- Implementing the CPEC by itself is not going to be easy as announcing the grant of funds because physically making the connections on the ground between China and Pakistan is going to pose a stiff challenge given the state of internal security in Pakistan.
- And then there is debate on the route of the CPEC itself as Pakistan wants it to pass through the more prosperous Punjab and not through Khyber Pakhtunkhwa (KPK), formerly known as North-West Frontier Province (NWFP).
Connecting the Dots
- Will One Belt and Initiative Increase the Domination of China In Asian Geopolitics?
- Explain Why India needs to be wary of China’s ambitious belt and road initiative?